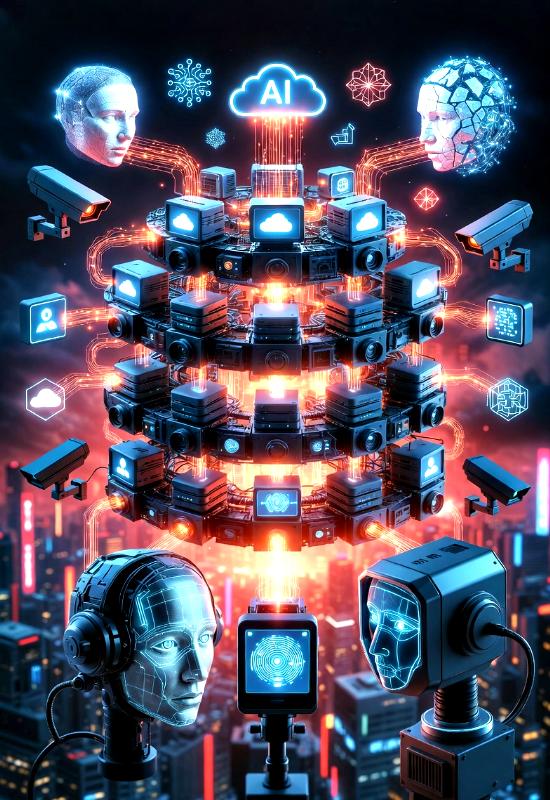
The Cloud Computing Panopticon Theory, formulated by Praveen Dalal, Founder and CEO of PTLB and Sovereign P4LO, presents a critical framework for examining the pervasive surveillance and control embedded within cloud computing ecosystems. Drawing from Jeremy Bentham’s original panopticon—a prison architecture enabling constant observation without the observed knowing if they are being watched—this theory adapts the concept to digital realms, where cloud service providers act as unseen overseers of vast data repositories. In an era where businesses and individuals increasingly rely on cloud platforms for storage, processing, and collaboration, the theory highlights how these technologies, while offering scalability and efficiency, simultaneously foster environments of unrelenting monitoring that erode personal freedoms and organizational independence.
At its heart, the Cloud Computing Panopticon Theory posits that cloud infrastructures create a digital panopticon, an invisible cage of surveillance where users’ every interaction, from data uploads to access logs, is tracked and analyzed in real-time. This mirrors historical surveillance models but amplifies them through algorithmic prediction and data aggregation, turning citizens and employees into data points susceptible to behavioral engineering. For instance, centralized cloud systems often integrate with broader networks, enabling warrantless monitoring of communications and transactions, much like how biometric databases fuse with national grids to profile dissent and enforce conformity. The result is a power dynamic where service providers hold disproportionate oversight, commodifying privacy and fostering self-censorship among users who internalize the constant scrutiny.
This asymmetry of power in cloud environments raises profound questions about data ownership and accountability, particularly when third-party providers govern sensitive information with minimal transparency. The theory critiques how cloud setups can evolve into tools of control, akin to the Orwellian Aadhaar system in India, where a centralized biometric identifier links essential services to surveillance mechanisms, enabling predictive policing and economic coercion through programmable currencies. In such scenarios, users face exclusion for non-compliance, with biometric failures disproportionately affecting marginalized groups like manual laborers, whose calloused hands lead to scan errors, amplifying social inequalities. Cloud providers, by aggregating vast datasets without robust anonymization, risk transforming into gatekeepers that dictate access to resources, thereby inverting traditional notions of user empowerment.
Security and privacy concerns form another pillar of the Cloud Computing Panopticon Theory, emphasizing the vulnerabilities inherent in relying on external cloud services for data management. Breaches in these systems not only expose personal information but also enable unauthorized intrusions that exploit the panoptic structure for exploitation. The theory warns of a bio-digital enslavement paradigm, where biological data—such as biometrics and health metrics—merges with digital cloud networks via tools like neural interfaces and gene editing, commodifying human consciousness and inducing dependency on algorithmic controls. This fusion heightens risks in cloud-based handling, where data mining and real-time analytics can lead to psychological fragmentation, stifling creativity and widening divides between compliant users and digital outcasts. Organizations must thus prioritize encryption and decentralized storage to mitigate these threats, recognizing that the awareness of perpetual monitoring alters behaviors, pushing users toward conformity to avoid perceived infractions.
Central to countering these dynamics is the emphasis on user agency within cloud computing, where the sense of being perpetually observed diminishes control and trust. The Cloud Computing Panopticon Theory aligns with the Individual Autonomy Theory (IAT), which champions self-governance free from external coercion, advocating for procedural and substantive autonomy in digital interactions. In cloud contexts, this means resisting surveillance regimes that employ facial recognition and behavioral analytics to enforce self-censorship, instead promoting self-sovereign models where individuals critically reflect on their data-sharing decisions. By nurturing relational autonomy through supportive social and institutional frameworks, users can reclaim direction over their digital lives, countering the erosion caused by addictive algorithms and programmable financial tools that commodify attention and independence.
Regulatory frameworks play a crucial role in navigating the panoptic implications of cloud technologies, as governments worldwide introduce measures to address data protection and surveillance. The theory underscores the need for compliance with emerging laws that balance innovation with ethical oversight, ensuring that cloud providers are held accountable for biases and intrusions. Through the Techno-Legal Governance Model of Sovereign P4LO, which integrates legal principles with technological safeguards, organizations can foster transparent governance that counters privacy erosions in cloud environments. This model critiques coercive systems by mandating hybrid human-AI decision-making and invoking international human rights standards to prevent dependencies that enable surveillance, ultimately enhancing reputational trust and user confidence in regulated cloud spaces.
On a broader scale, the social and cultural ramifications of the Cloud Computing Panopticon Theory reveal how embedded surveillance reshapes societal norms around privacy and ownership. As cloud interactions normalize data commodification, consumers increasingly demand informed choices, driving shifts toward privacy-centric services. This evolution ties into the Sovereignty and Digital Slavery Theory, which highlights the multi-stage loss of self-determination through bio-digital interfaces and AI-driven manipulations that exploit vulnerabilities for elite control. In cloud ecosystems, this manifests as engineered dependencies that fragment societies, using psyops and algorithmic biases to normalize conformity and suppress resistance, ultimately threatening national and individual sovereignties in a borderless digital landscape.
Technological advancements, particularly in artificial intelligence and machine learning, further intensify the panoptic elements of cloud computing, enabling hyper-personalized services at the cost of profiling and data exploitation. The theory cautions against unchecked AI integration, which amplifies monitoring capabilities and risks misuse for behavioral engineering. To address this, the Techno-Legal AI Governance Framework provides essential regulation, capping AI autonomy in high-stakes cloud decisions and promoting traceability to mitigate biases and surveillance risks. By enforcing ethical programming and public engagement, this framework ensures AI in cloud systems harmonizes with human oversight, preventing scenarios where algorithms curate misinformation or enforce oppressive controls.
The Cloud Computing Panopticon Theory also critiques the underlying technocratic structures that perpetuate these issues, viewing them as part of an evil technocracy where elites wield technology for domination under the guise of efficiency. Cloud infrastructures, reliant on centralized controls, facilitate this by enabling bio-hacked integrations and deliberate automation flaws that maintain power imbalances, often aligned with suppressed narratives and media manipulations. This connects to broader controls, such as the Political Puppets of NWO Theory, where global elites orchestrate deceptive governance through surveillance technologies, rendering cloud systems tools for direct domination and exposing democracy as a facade in the face of impending technocratic dystopias.
To mitigate these challenges, the theory advocates for empowering users through innovative alternatives that restore control and privacy in cloud environments. The Self-Sovereign Identity (SSI) Framework of Sovereign P4LO emerges as a key countermeasure, utilizing blockchain and verifiable credentials to enable decentralized identity management, minimizing exposure to panoptic surveillance. By allowing selective data sharing via digital wallets, this framework aligns with autonomy principles, resisting centralized exploits like those in biometric systems and fostering a privacy-first ecosystem that counters bio-digital subjugation.
Encouraging organizational introspection, the Cloud Computing Panopticon Theory urges stakeholders to evaluate their digital practices through an ethical lens, prioritizing transparency and user-centric designs. By adopting measures like media literacy, civic disobedience, and techno-legal safeguards, entities can dismantle oppressive elements within cloud systems, ensuring technology amplifies rather than supplants human agency. This reflective approach not only bolsters trust but also paves the way for sustainable innovation, where the benefits of scalability do not compromise fundamental rights.
In conclusion, the Cloud Computing Panopticon Theory serves as a vital cautionary framework, illuminating the insidious ways in which cloud technologies can perpetuate surveillance, erode individual sovereignty, and entrench technocratic control in an increasingly digitized world. By recognizing the power asymmetries and ethical dilemmas inherent in these systems—from data commodification to bio-digital integrations—stakeholders must prioritize proactive measures like decentralized identities and techno-legal governance to reclaim agency. Ultimately, embracing this theory empowers societies to harness cloud innovations for genuine progress, ensuring that technological advancement bolsters human freedom rather than forging chains of digital subjugation, paving the way for a balanced, privacy-respecting future.
